🔐 **A Deep Dive into Data Encryption: Best Practices for Data Security**
In today’s digital landscape, securing data at all levels is non-negotiable. One of the most effective ways to ensure data safety is through **encryption**. Let’s break down the main types of data encryption and highlight their importance:
### 1. **Full-Disk Encryption**
Full-disk encryption (FDE) protects data-at-rest by encrypting the entire storage device. This ensures that unauthorized users cannot access data even if they gain physical control of the device. Common tools include **BitLocker for Windows** and **FileVault for macOS**. FDE is essential for safeguarding sensitive information in cases of lost or stolen devices.
### 2. **File System Encryption**
Unlike full-disk encryption, **file system encryption** targets specific files and folders. This method allows for granular control, protecting only selected data instead of the whole disk. It is beneficial for multi-user environments where not all data needs to be encrypted. Common solutions include **EFS (Encrypting File System)** on Windows.
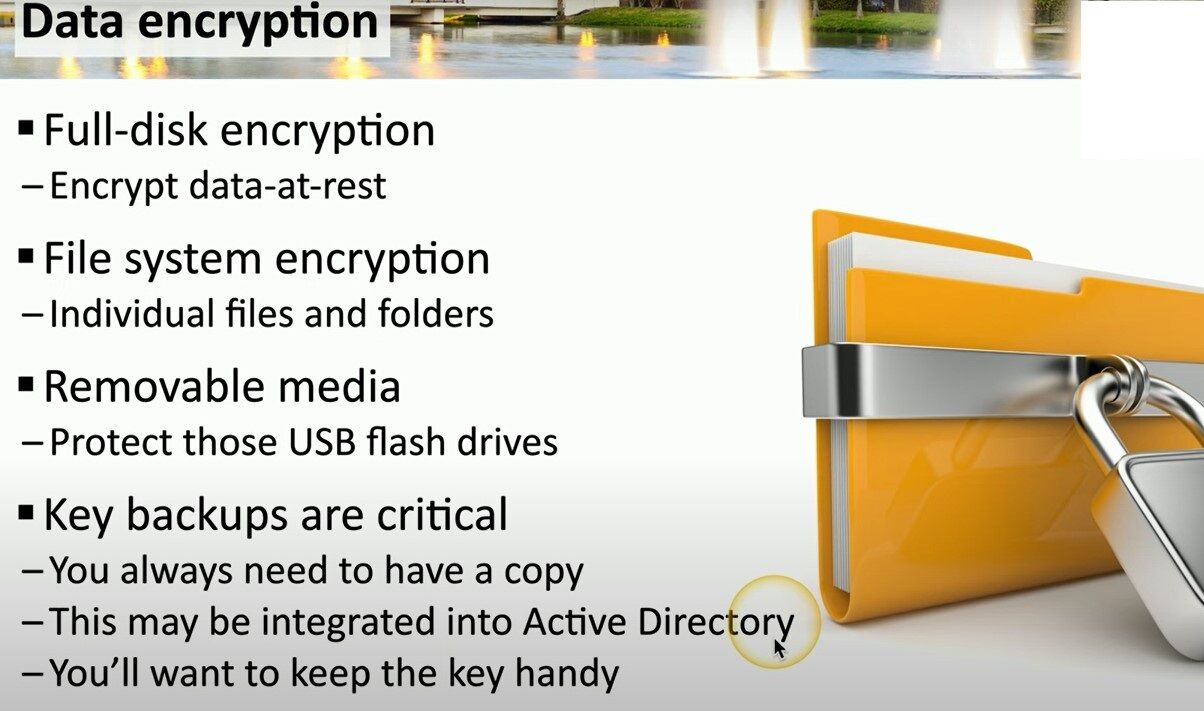
### 3. **Encryption for Removable Media**
With the proliferation of portable data storage devices, such as USB flash drives, securing removable media is critical. Encryption software designed for removable storage ensures that data remains protected when transferred or transported.
Tools like **VeraCrypt** or native solutions like BitLocker’s removable media encryption offer effective protection.
### 4. **Key Backup Importance**
A vital yet sometimes overlooked aspect of encryption is key management. **Key backups** are crucial because losing an encryption key means losing access to the data. Key backups can be integrated into centralized management systems like **Active Directory** to streamline access and recovery processes. Always store backup keys in a secure, separate location to minimize risk.
### Why It Matters:
Whether it’s comprehensive full-disk encryption, selective file-level encryption, or protecting data on removable media, maintaining an efficient encryption strategy helps prevent unauthorized access and ensures data integrity.
**Key management** and having backups of encryption keys are just as critical, as they are the linchpins in ensuring data recovery and accessibility when needed.
#DataEncryption #CyberSecurity #DigitalSafety


Leave a comment