In June 2017, security researcher Aaron Guzman uncovered a critical vulnerability in Subaru’s web authentication system. When users authenticate with Subaru, they receive a token that never expires – a significant security flaw.
This perpetual token granted unfettered access to any service request, including adding one’s email to someone else’s account, effectively allowing full control over another person’s car.
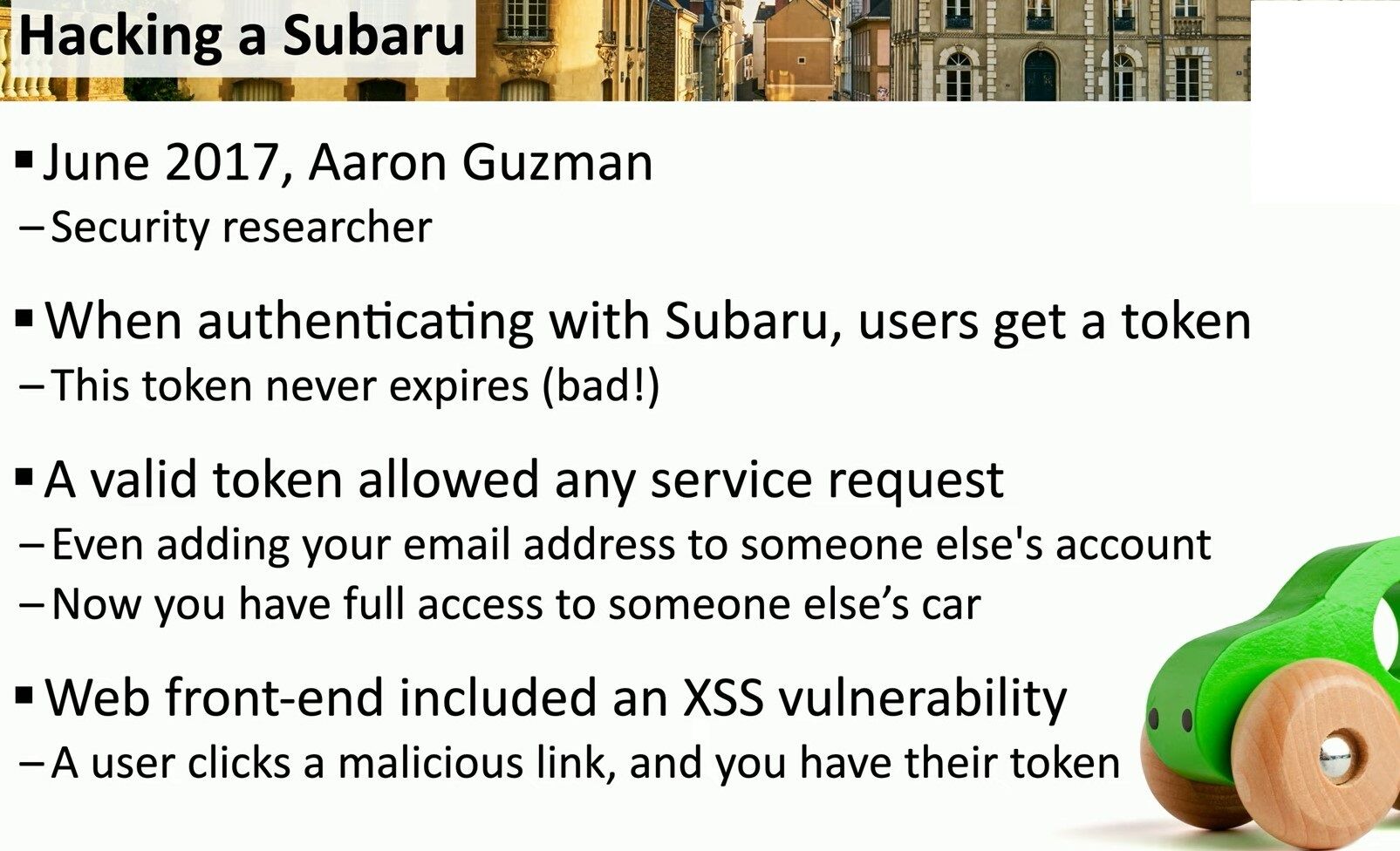
To make matters worse, Subaru’s web front-end was susceptible to a Cross-Site Scripting (XSS) attack. In such an attack, an unsuspecting user clicks a malicious link, enabling the attacker to capture their authentication token.
With this token, the attacker could gain complete access to the victim’s account, exploiting the token’s indefinite lifespan to perform unauthorized actions indefinitely.
Cross-Site Scripting (XSS) attacks occur when an attacker injects malicious scripts into content from otherwise trusted websites. These scripts are executed in the victim’s browser, allowing the attacker to steal information, manipulate web sessions, or deface websites.
XSS exploits the trust a user’s browser has in a website, making it a powerful tool for attackers.
This incident underscores the importance of implementing expiring tokens and securing web applications against XSS vulnerabilities. By addressing these issues, companies can better protect their users from potentially severe security breaches.
#CyberSecurity #XSSAttack



Leave a comment